In this lab, you will create the spoke virtual network and create a secured virtual hub, then you will connect the hub and spoke virtual networks and route traffic to your hub. Next you will deploy the workload servers, then create a firewall policy and secure your hub, and finally you will test the firewall.
Create a hub and spoke architecture
In this part of the lab, you will create the spoke virtual networks and subnets where you will place the workload servers. Then you will create the secured virtual hub and connect the hub and spoke virtual networks.
In this lab, you will:
- Task 1: Create two spoke virtual networks and subnets
- Task 2: Create the secured virtual hub
- Task 3: Connect the hub and spoke virtual networks
- Task 4: Deploy the servers
- Task 5: Create a firewall policy and secure your hub
- Task 6: Associate the firewall policy
- Task 7: Route traffic to your hub
- Task 8: Test the application rule
- Task 9: Test the network rule
Prerequisites for this labs : Azure Account / Download Labs Files here
Task 1: Create two spoke virtual networks and subnets
In this task, you will create the two spoke virtual networks each containing a subnet that will host your workload servers.
- On the Azure portal home page, in the search box, type virtual network and select Virtual Network when it appears.
- Click Create.
- In Resource group, select Create new, and enter fw-manager-rg as the name and click OK.
- In Name, enter Spoke-01.
- In Region, select your region.

- Click Next: IP Addresses.
- In IPv4 address space, enter 10.0.0.0/16.
- Delete any other address spaces listed here, such as 10.1.0.0/16.
- Under Subnet name, click the word default.
- In the Edit subnet dialog box, change the name to Workload-01-SN.
- Change the Subnet address range to 10.0.1.0/24.
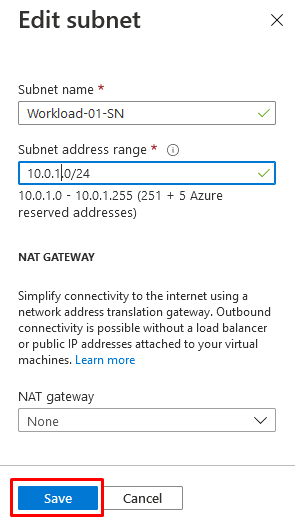
Click Save.
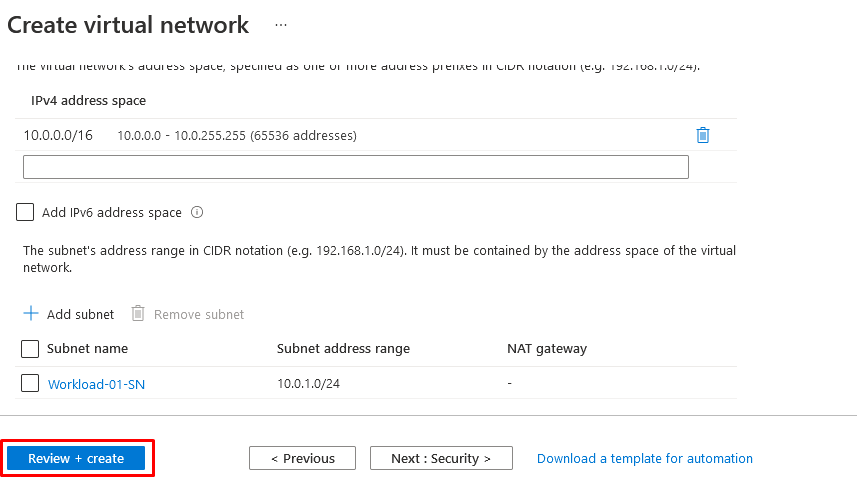
Click Review + create.
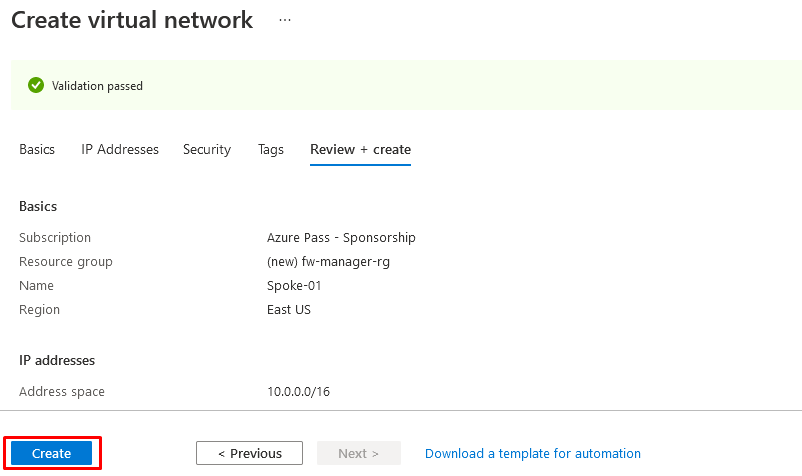
Click Create.
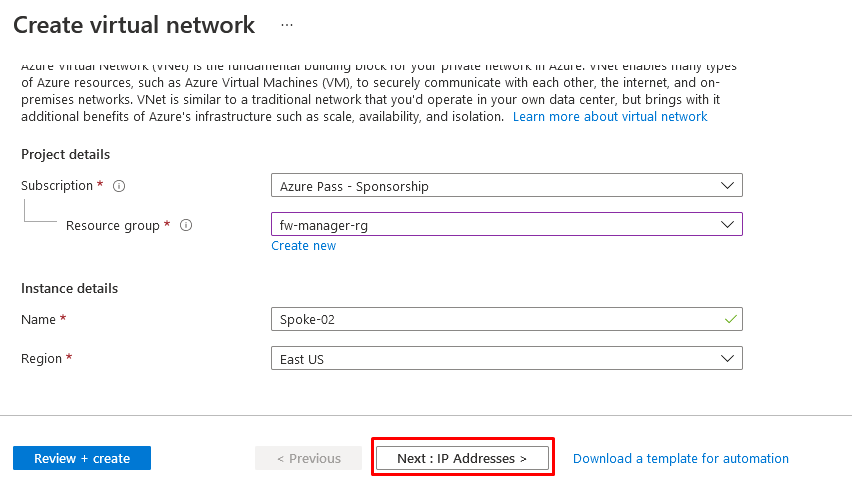
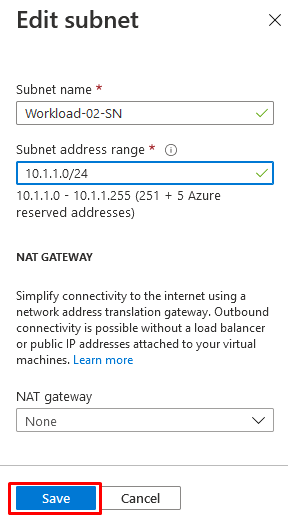
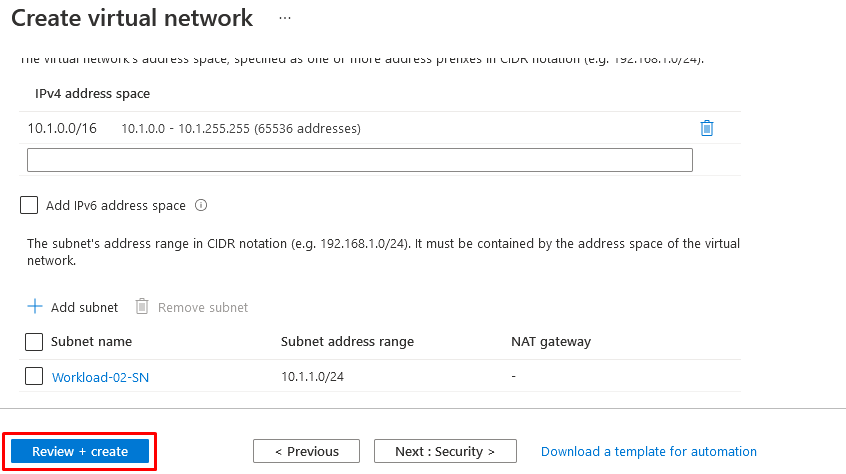
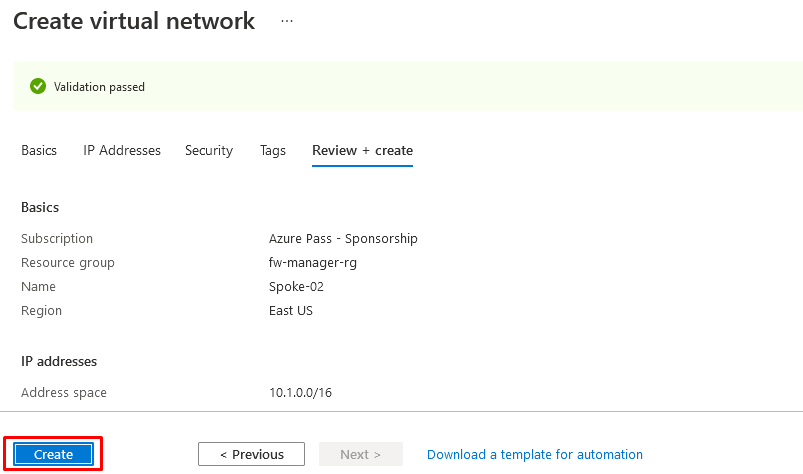
Repeat steps 1 to 14 above to create another similar virtual network and subnet but using the following information:
- Resource Group: fw-manager-rg (select existing)
- Name: Spoke-02
- Address space: 10.1.0.0/16 – (delete any other listed address spaces)
- Subnet name: Workload-02-SN
- Subnet address range: 10.1.1.0/24
Task 2: Create the secured virtual hub
In this task you will create your secured virtual hub using Firewall Manager.
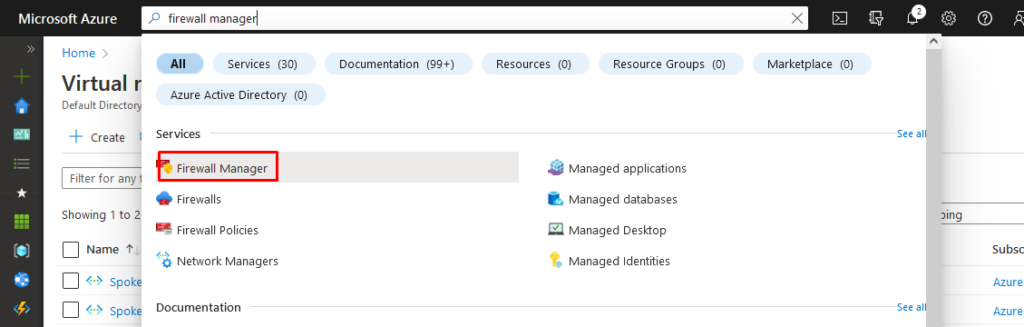
- From the Azure portal home page, click All services.
- In the search box, type firewall manager and select Firewall Manager when it appears.
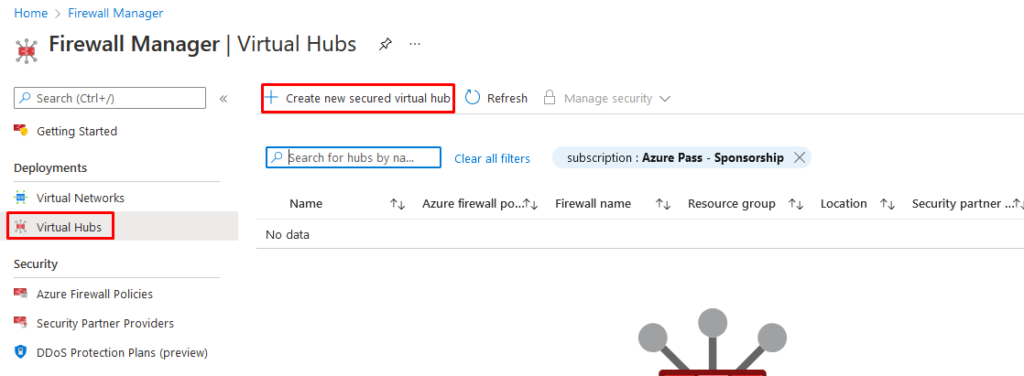
On the Firewall Manager page, from the Overview page, click View secured virtual hubs.

On the Virtual hubs page, click Create new secured virtual hub.
- For Resource group, select fw-manager-rg.
- For Region, select your region.
- For the Secured virtual hub name, enter Hub-01.
- For Hub address space, enter 10.2.0.0/16.
- Choose New vWAN.
- In Virtual WAN Name, enter Vwan-01.
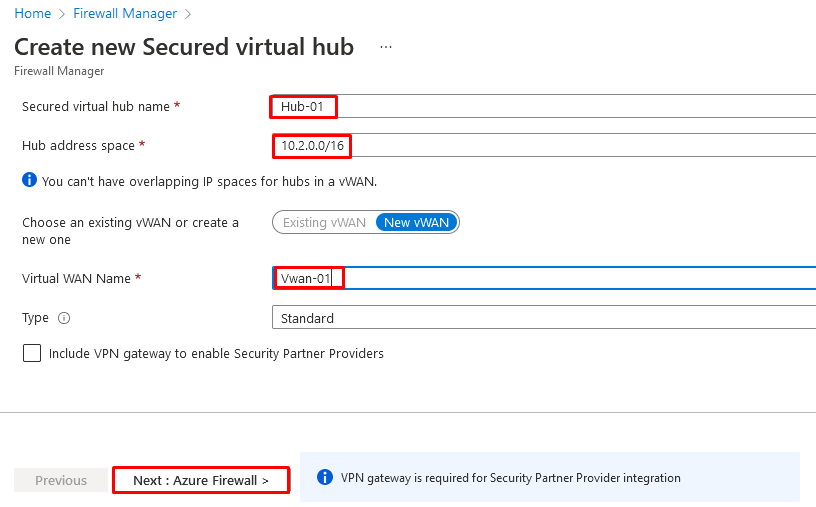
Click Next: Azure Firewall.
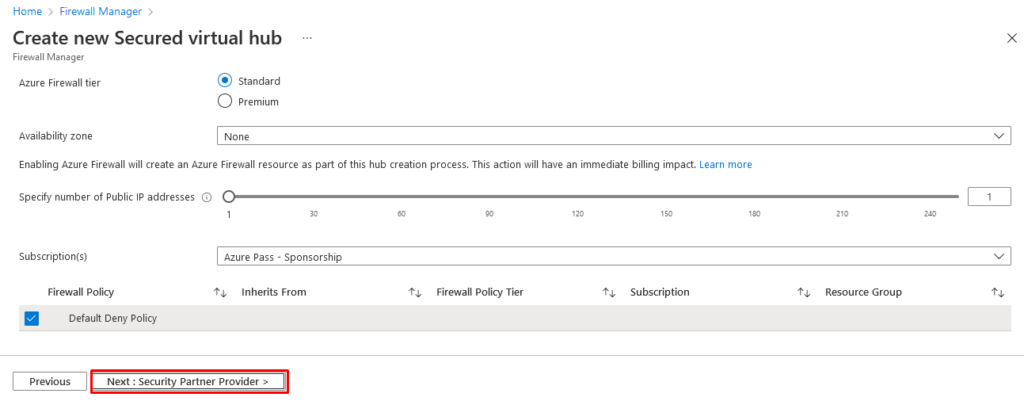
Click Next: Security Partner Provider.
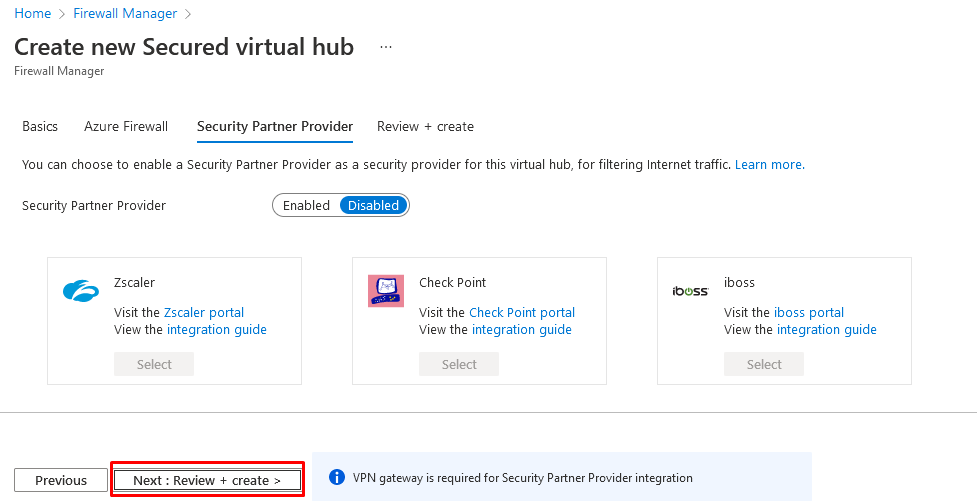
Click Next: Review + create.
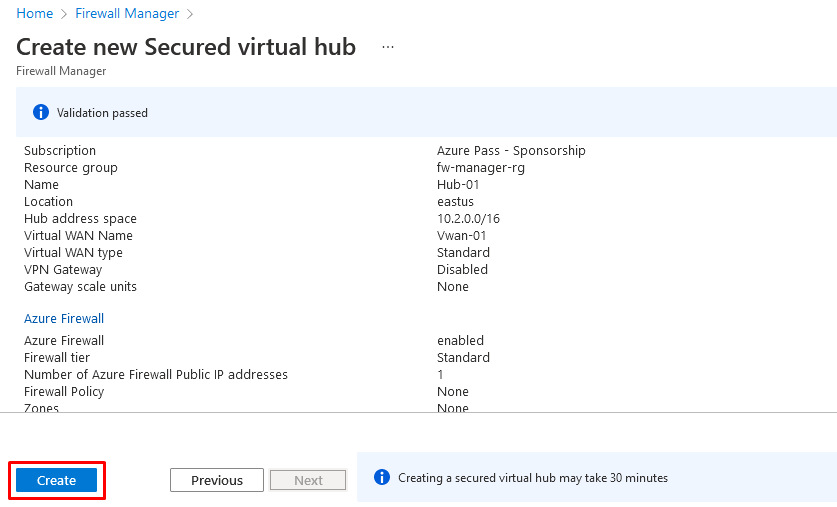
- Click Create.
[!NOTE]
This can take up to 30 minutes to deploy.
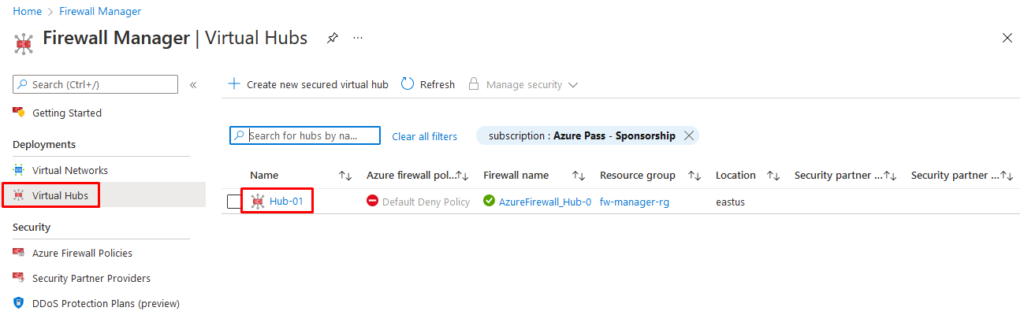
- When the deployment completes, from the Azure portal home page, click All services.
- In the search box, type firewall manager and select Firewall Manager when it appears.
- On the Firewall Manager page, click Virtual hubs.
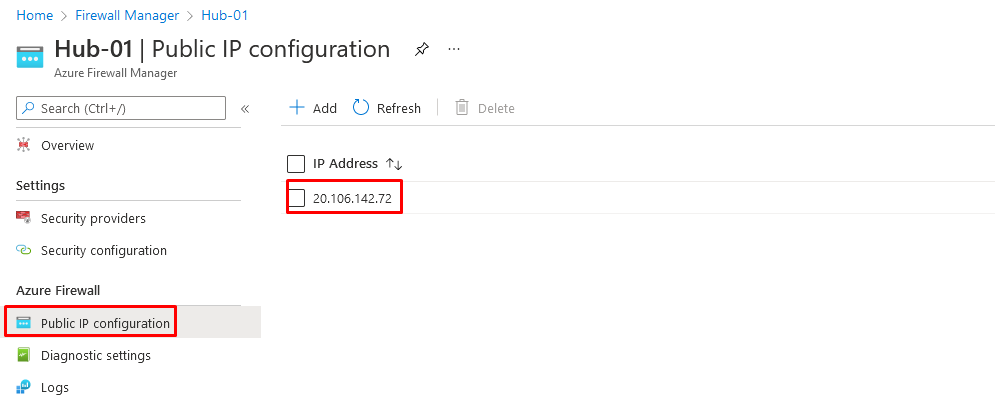
- Click Hub-01.
- Click Public IP configuration.
- Note down the public IP address (e.g., 20.106.142.72), which you will use later.
Task 3: Connect the hub and spoke virtual networks
In this task you will connect the hub and spoke virtual networks. This is commonly known as peering.
- From the Azure portal home page, click Resource groups.
- Select the fw-manager-rg resource group, then select the Vwan-01 virtual WAN.
- Under Connectivity, click Virtual network connections.
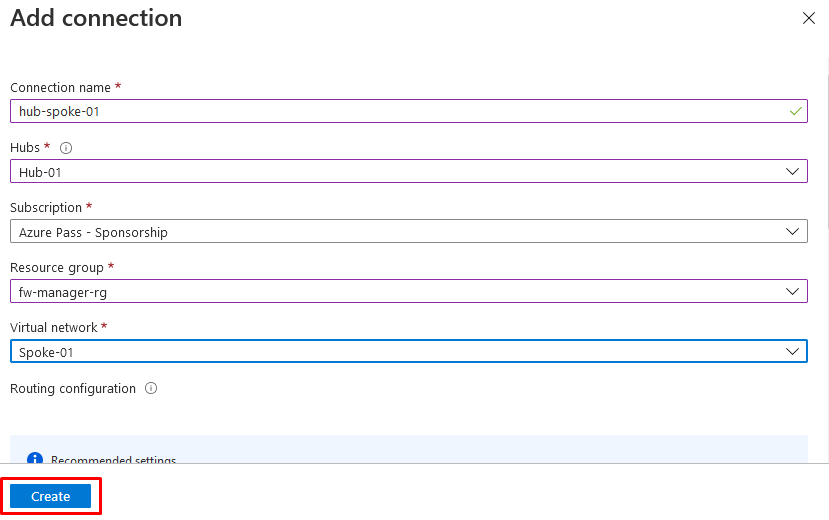
- Click Add connection.
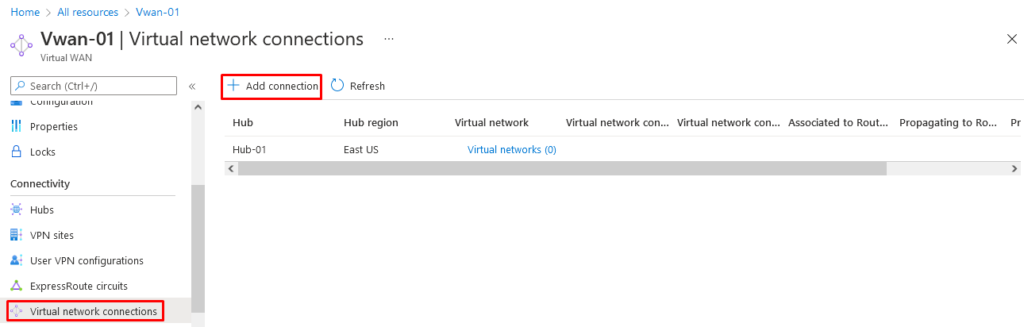
- For Connection name, enter hub-spoke-01.
- For Hubs, select Hub-01.
- For Resource group, select fw-manager-rg.
- For Virtual network, select Spoke-01.
- Click Create.
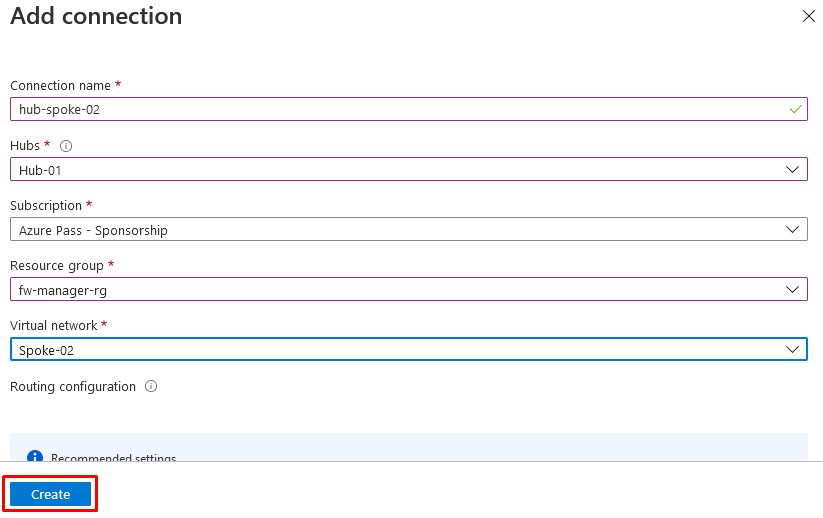
Repeat steps 4 to 9 above to create another similar connection but using the connection name of hub-spoke-02 to connect the Spoke-02 virtual network.
Task 4: Deploy the servers
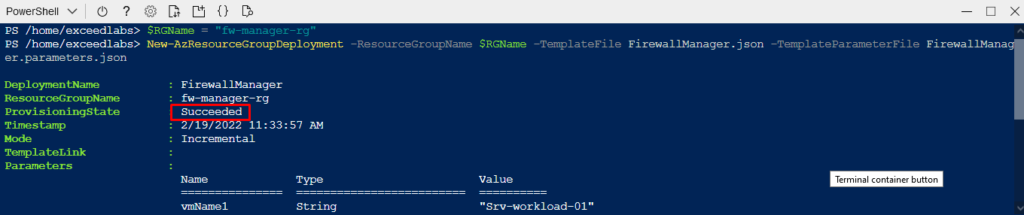
- In the Azure portal, open the PowerShell session within the Cloud Shell pane.
- In the toolbar of the Cloud Shell pane, select the Upload/Download files icon, in the drop-down menu, select Upload and upload the following files FirewallManager.json and FirewallManager.parameters.json into the Cloud Shell home directory from the source folder F:\Allfiles\Labs\M06.
- Deploy the following ARM templates to create the VM needed for this lab:
code
$RGName = "fw-manager-rg"
New-AzResourceGroupDeployment -ResourceGroupName $RGName -TemplateFile FirewallManager.json -TemplateParameterFile FirewallManager.parameters.json
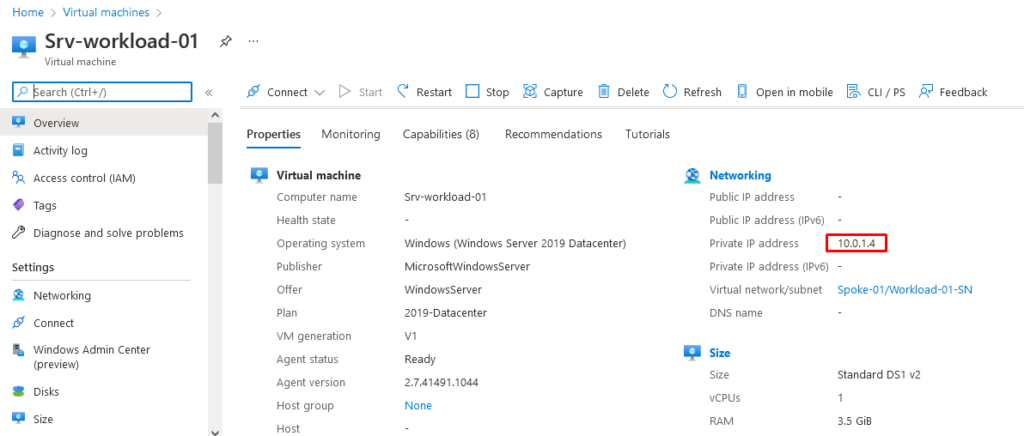
- When the deployment is complete, go to the Azure portal home page, and then select Virtual Machines.
- On the Overview page of Srv-workload-01, in the right-hand pane, under the Networking section, note down the Private IP address (e.g., 10.0.1.4).
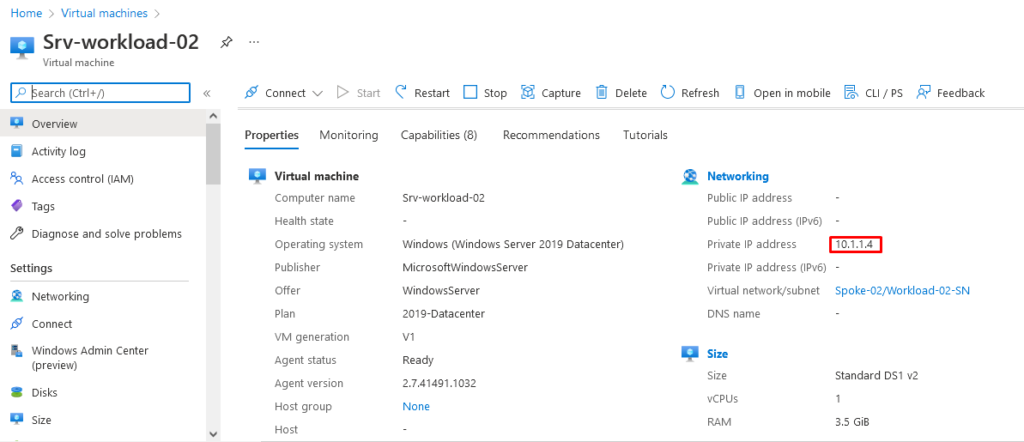
On the Overview page of Srv-workload-02, in the right-hand pane, under the Networking section, note down the Private IP address (e.g., 10.1.1.4).
Task 5: Create a firewall policy and secure your hub
In this task you will first create your firewall policy, then secure your hub. The firewall policy will define collections of rules to direct traffic on one or more Secured virtual hubs.
- From the Azure portal home page, click Firewall Manager.
- If the Firewall Manager icon does not appear on the homepage, then click All services. Then in the search box, type firewall manager and select Firewall Manager when it appears.
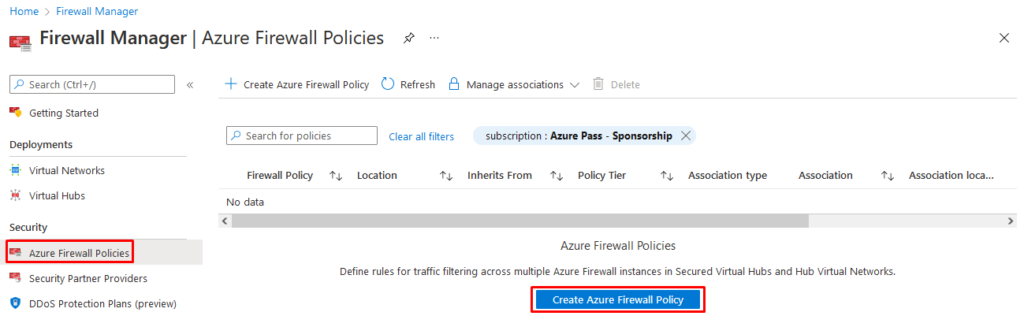
- From Firewall Manager, from the Overview page, click View Azure Firewall Policies.
- Click Create Azure Firewall Policy.
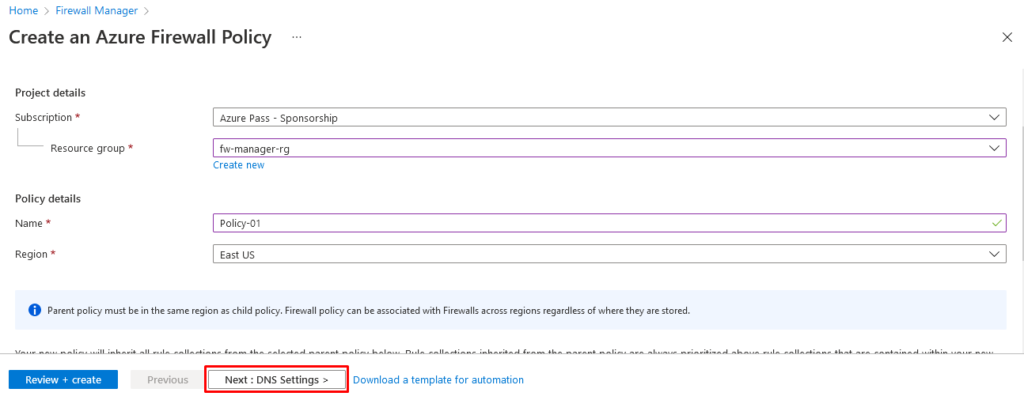
- In Resource group, select fw-manager-rg.
- Under Policy details, for the Name, enter Policy-01.
- In Region select your region.
- In Policy tier, select Standard.
- Click Next : DNS Settings.
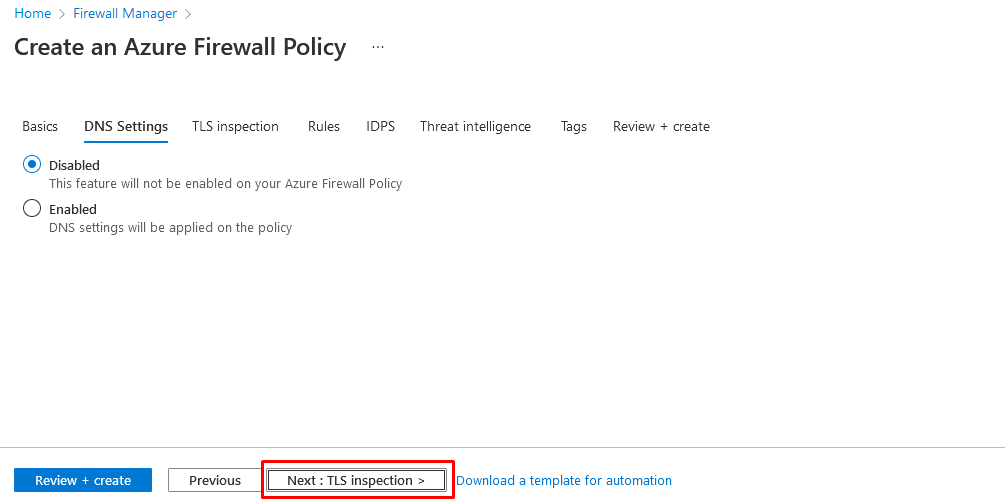
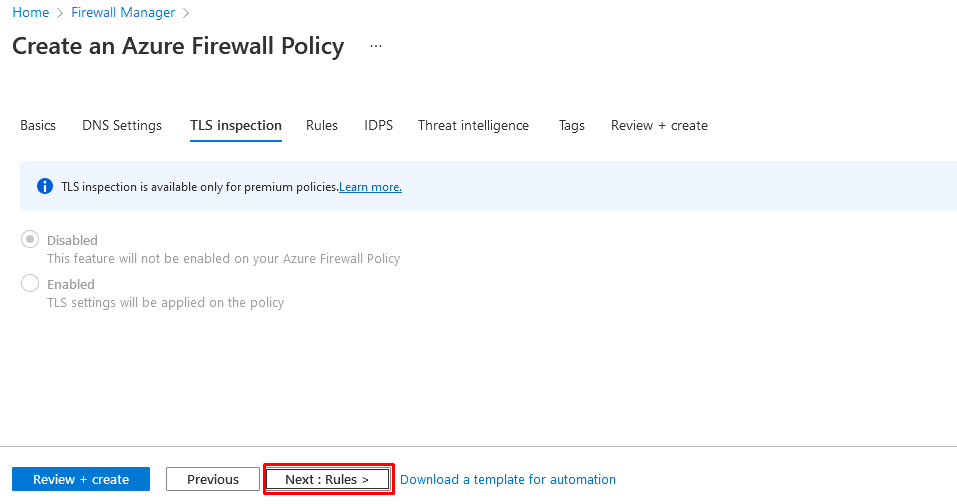
Click Next : TLS Inspection (preview).
Click Next : Rules.
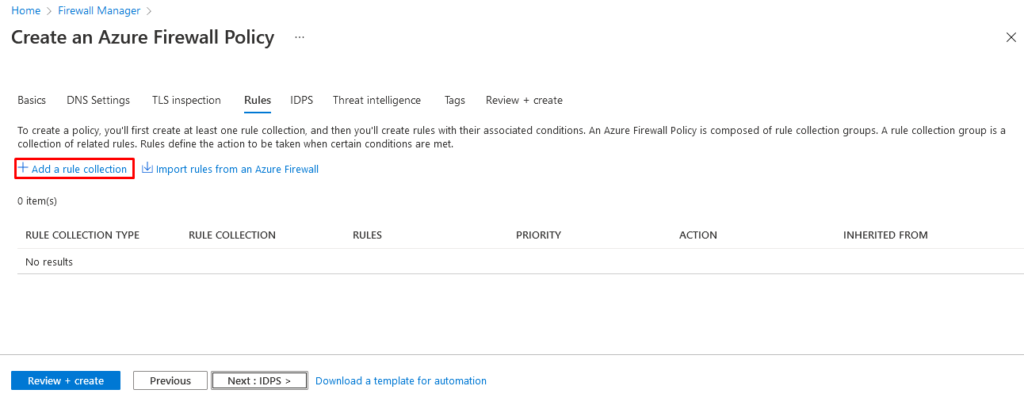
On the Rules tab, click Add a rule collection.
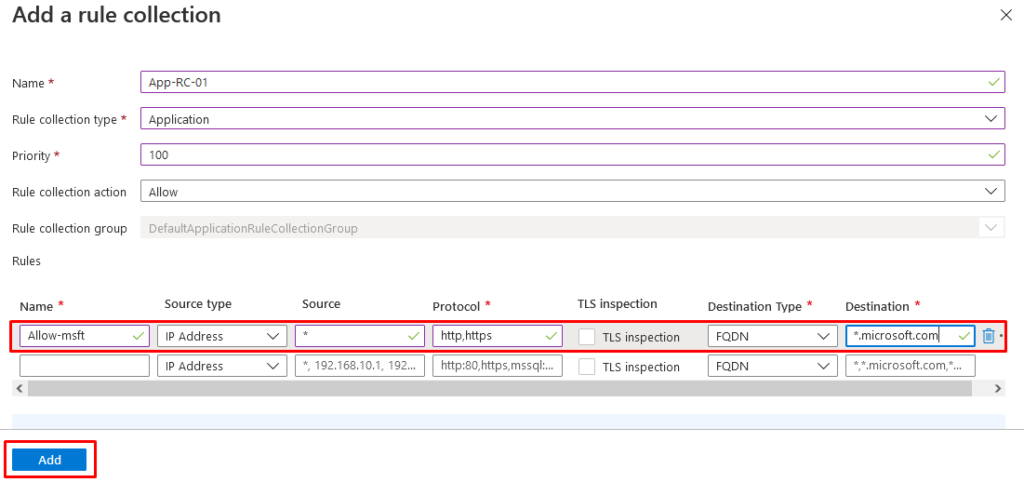
- On the Add a rule collection page, in Name, enter App-RC-01.
- For Rule collection type, select Application.
- For Priority, enter 100.
- Ensure Rule collection action is Allow.
- Under Rules, in Name type Allow-msft.
- For the Source type, select IP Address.
- For Source, enter *.
- For Protocol, enter http,https.
- Ensure Destination type is FQDN.
- For Destination, enter *.microsoft.com.
- Click Add.
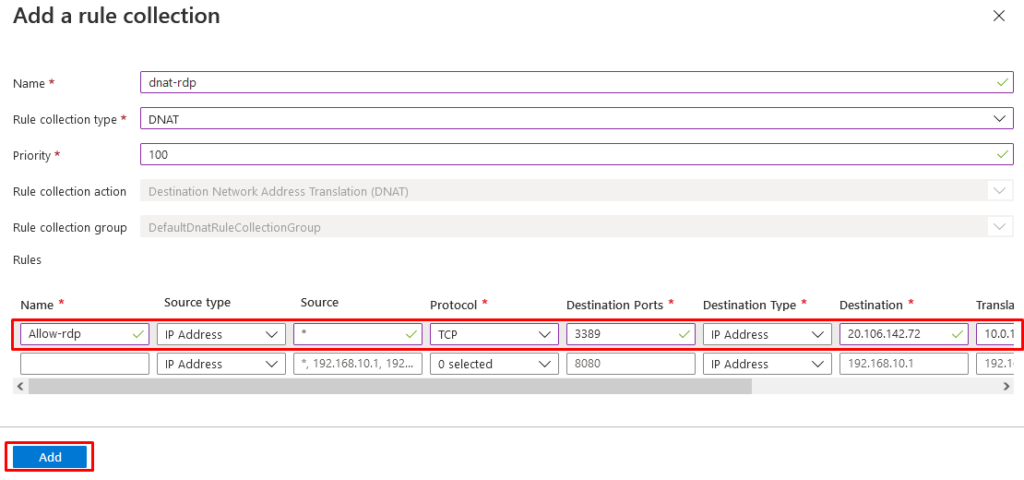
- To add a DNAT rule so you can connect a remote desktop to the Srv-workload-01 VM, click Add a rule collection.
- For Name, enter dnat-rdp.
- For Rule collection type, select DNAT.
- For Priority, enter 100.
- Under Rules, in Name enter Allow-rdp.
- For the Source type, select IP Address.
- For Source, enter *.
- For Protocol, select TCP.
- For Destination Ports, enter 3389.
- For Destination Type, select IP Address.
- For Destination, enter the firewall virtual hub public IP address that you noted down earlier (e.g., 51.143.226.18).
- For Translated address, enter the private IP address for Srv-workload-01 that you noted down earlier (e.g., 10.0.1.4).
- For Translated port, enter 3389.
- Click Add.
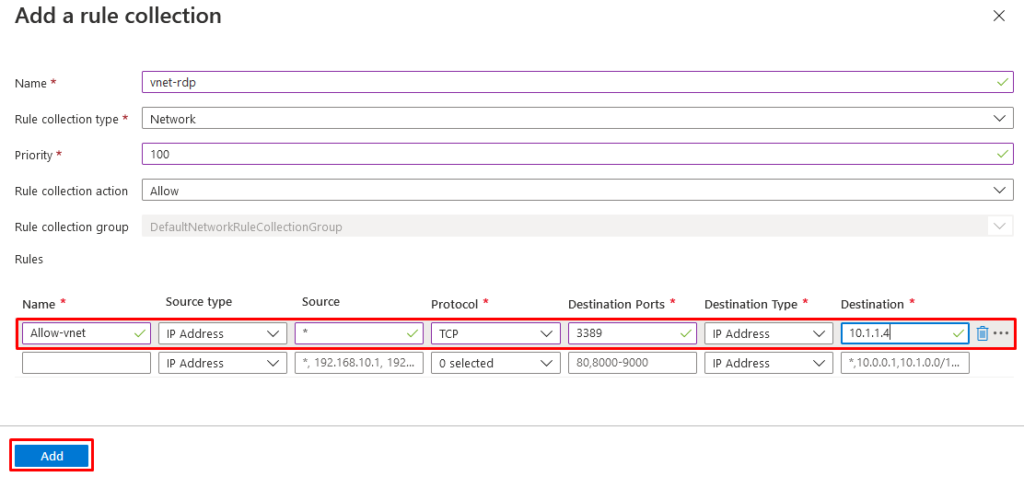
- To add a Network rule so you can connect a remote desktop from Srv-workload-01 to Srv-workload-02 VM, click Add a rule collection.
- For Name, enter vnet-rdp.
- For Rule collection type, select Network.
- For Priority, enter 100.
- For Rule collection action, select Allow.
- Under Rules, in Name enter Allow-vnet.
- For the Source type, select IP Address.
- For Source, enter *.
- For Protocol, select TCP.
- For Destination Ports, enter 3389.
- For Destination Type, select IP Address.
- For Destination, enter the private IP address for Srv-workload-02 that you noted down earlier (e.g., 10.1.1.4).
- Click Add.
You should now have 3 rule collections listed.
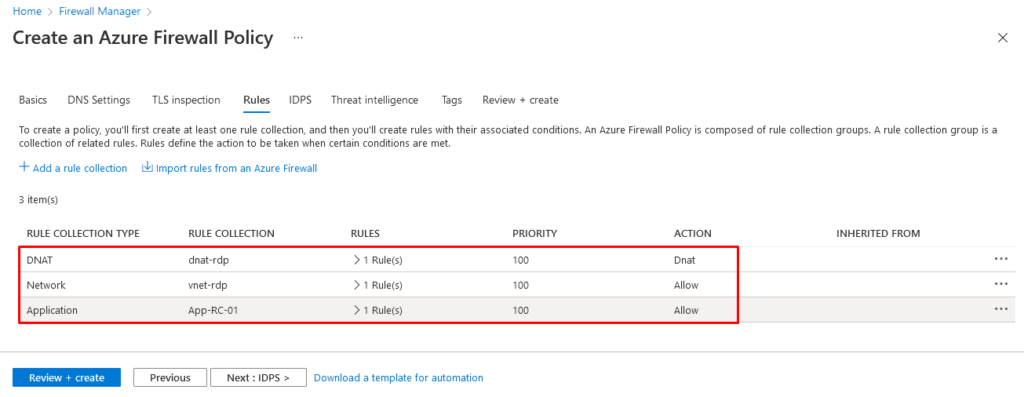
Click Review + create.
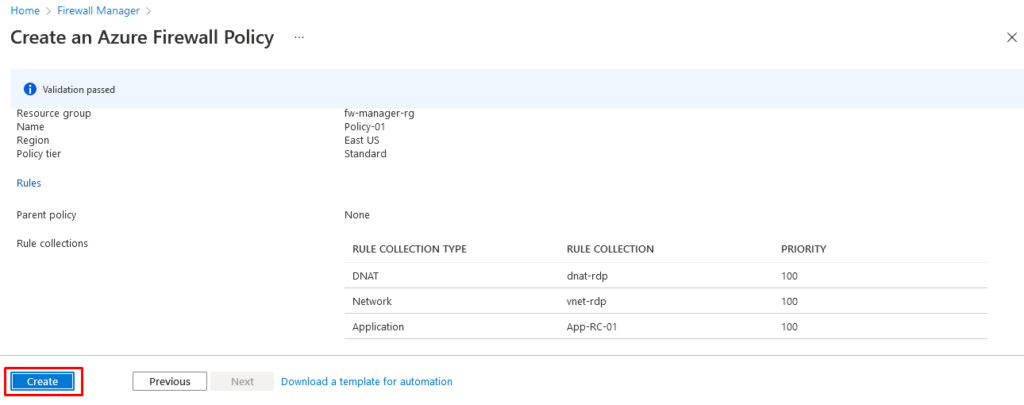
Click Create.
Task 6: Associate the firewall policy
In this task you will associate the firewall policy with the virtual hub.
- From the Azure portal home page, click Firewall Manager.
- If the Firewall Manager icon does not appear on the homepage, then click All services. Then in the search box, type firewall manager and select Firewall Manager when it appears.
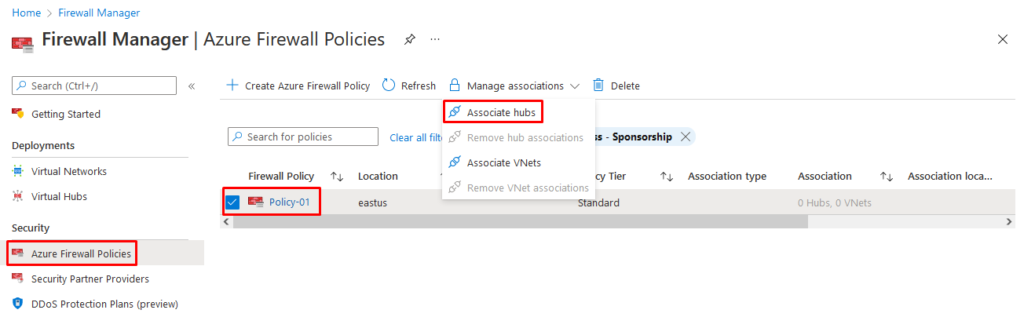
- In Firewall Manager, under Security, click Azure Firewall Policies.
- Select the checkbox for Policy-01.
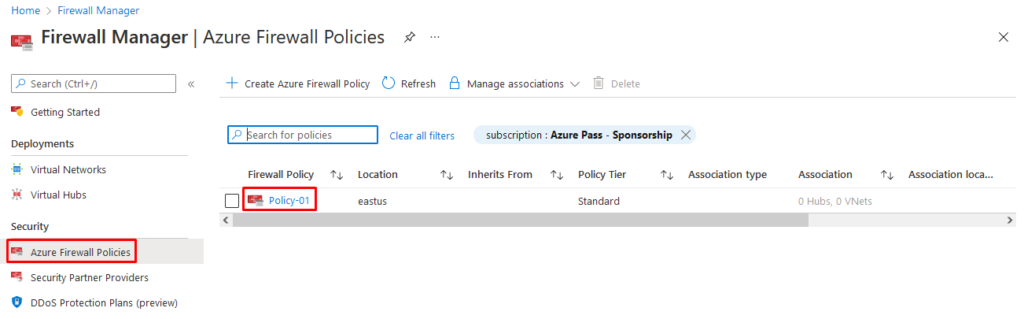
Select Manage associations>Associate hubs.
- Select the checkbox for Hub-01.
- Click Add.
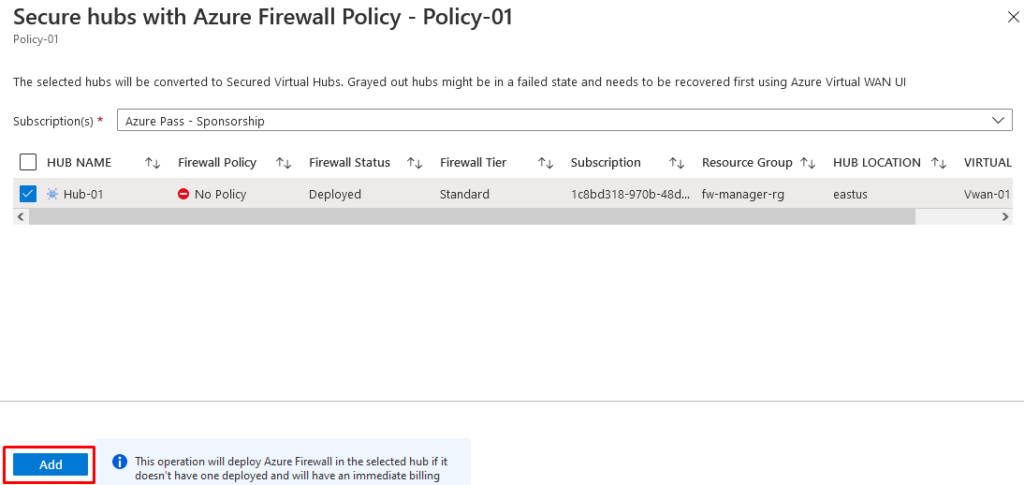
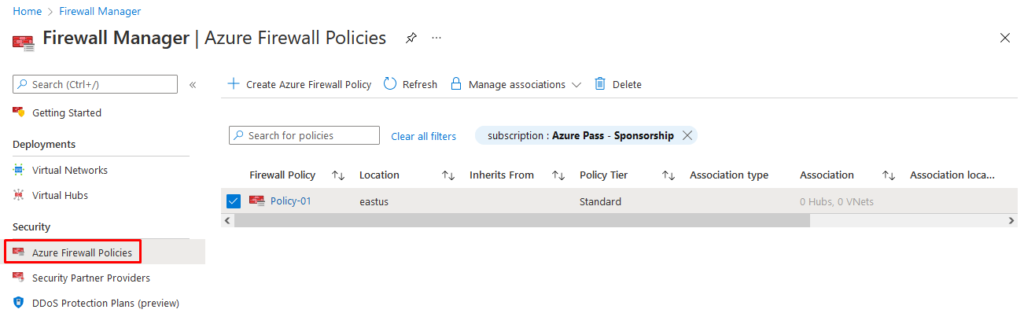
When the policy has been attached, click Refresh. The association should be displayed.
Task 7: Route traffic to your hub
In this task you will ensure that network traffic gets routed through your firewall.
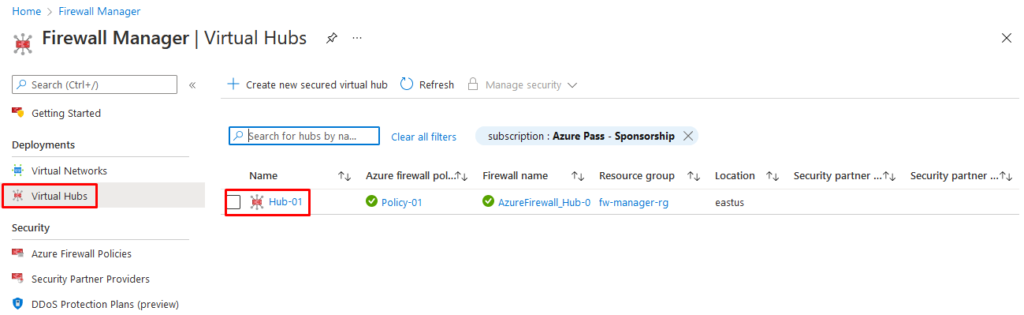
- In Firewall Manager, click Virtual hubs.
- Click Hub-01.
- Under Settings, click Security configuration.
- In Internet traffic, select Azure Firewall.
- In Private traffic, select Send via Azure Firewall.
- Click Save.
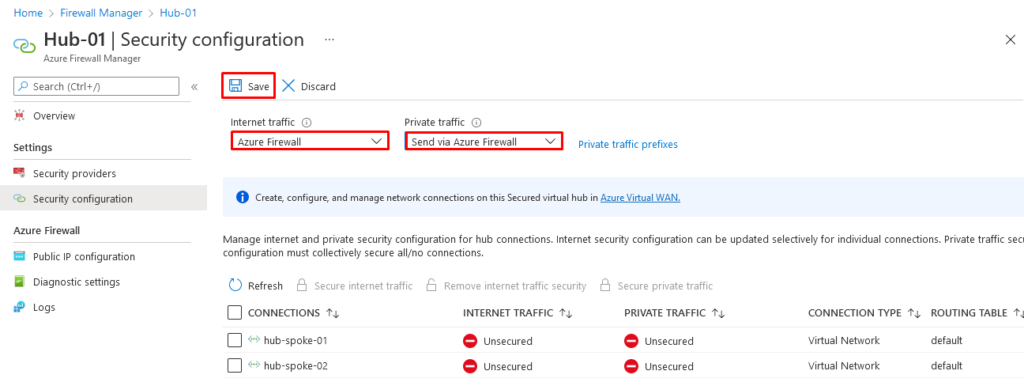
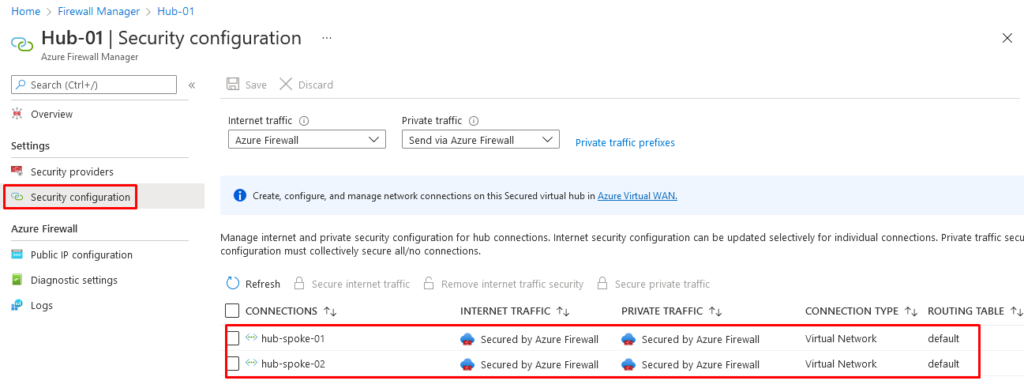
- This will take a few minutes to complete.
- Once configuration has completed, ensure that under INTERNET TRAFFIC and PRIVATE TRAFFIC, it says Secured by Azure Firewall for both hub-spoke connections.
Task 8: Test the application rule
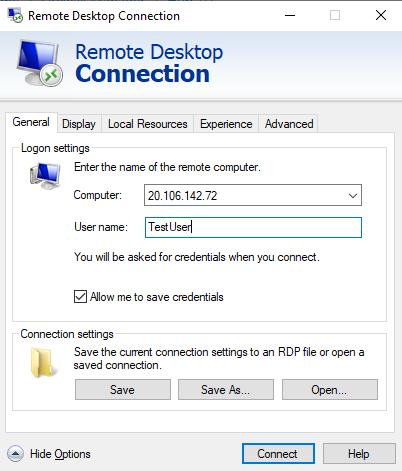
In this part of the lab, you will connect a remote desktop to the firewall public IP address, which is NATed to Srv-Workload-01. You will then use a web browser to test the application rule and connect a remote desktop to Srv-Workload-02 to test the network rule.
In this task you will test the application rule to confirm that it works as expected.
- Open Remote Desktop Connection on your PC.
- In the Computer box, enter the firewall’s public IP address (e.g., 20.106.142.72).
- Click Show Options.
- In the Username box, enter TestUser.
- Click Connect.
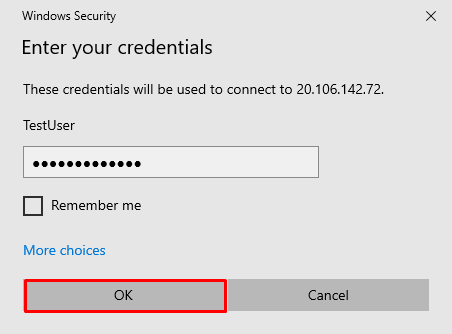
- In the Enter your credentials dialog box, log into the Srv-workload-01 server virtual machine, by using the password, TestPa$$w0rd!.
- Click OK.
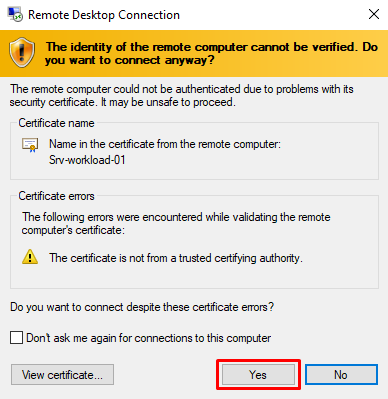
Click Yes on the certificate message.
- Open Internet Explorer and click OK in the Set up Internet Explorer 11 dialog box.
- Browse to https://www.microsoft.com.
- In the Security Alert dialog box, click OK.
- Click Close on the Internet Explorer security alerts that may pop-up.
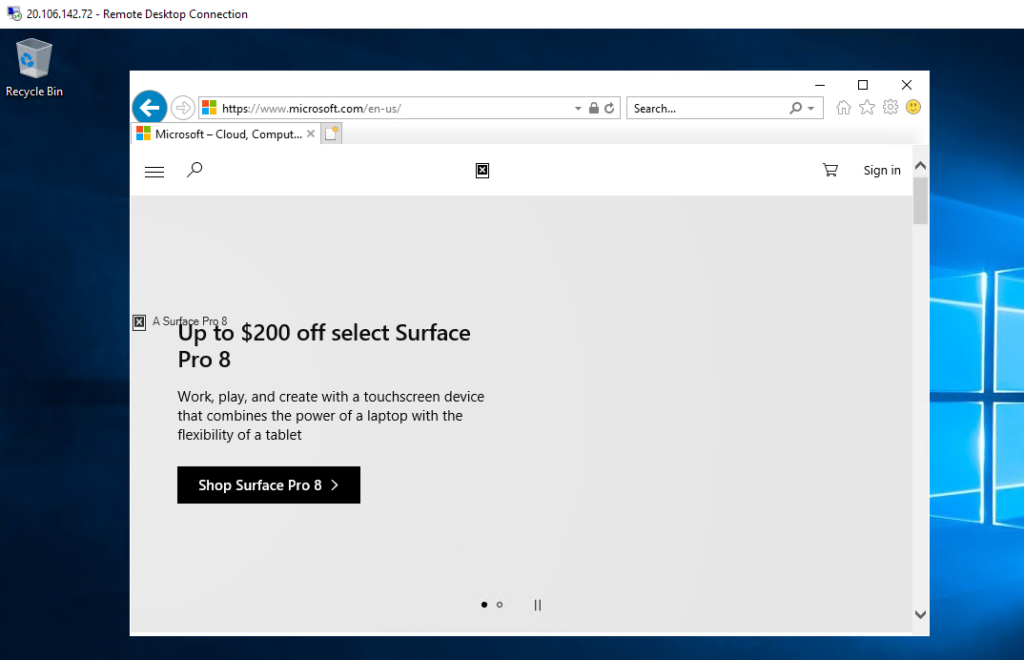
- You should see the Microsoft home page.
- Browse to https:// www.google.com.
- You should be blocked by the firewall.
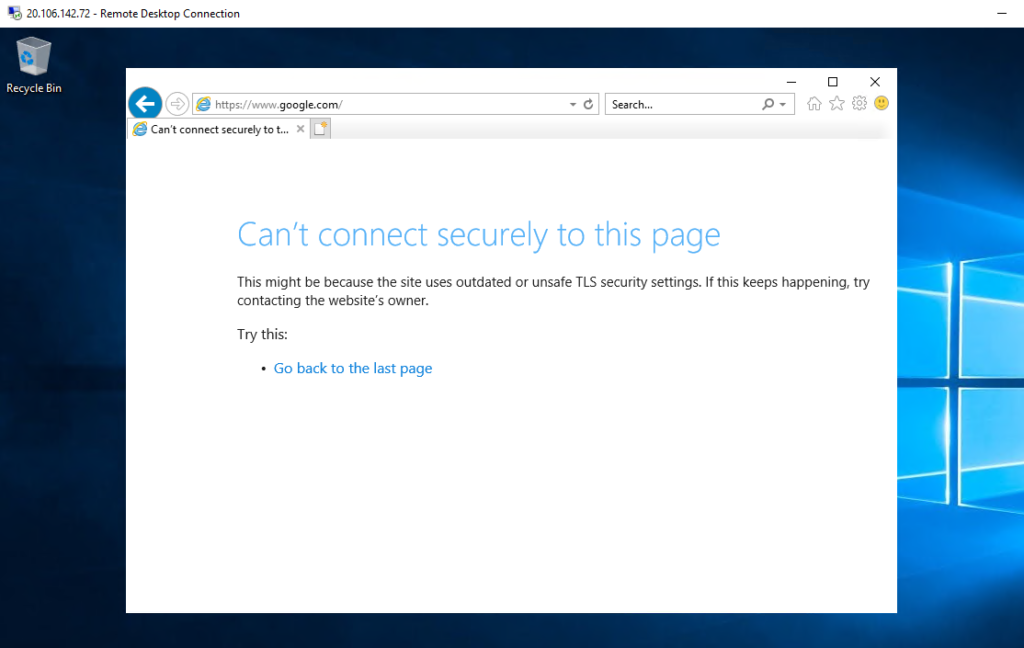
- So, you have verified that you can connect to the one allowed FQDN but are blocked from all others.
Task 9: Test the network rule
In this task you will test the network rule to confirm that it works as expected.
- While still logged in to the Srv-workload-01 RDP session, from this remote computer, open Remote Desktop Connection.
- In the Computer box, enter the private IP address of Srv-workload-02 (e.g., 10.1.1.4).
- In the Enter your credentials dialog box, log in to the Srv-workload-02 server by using the username TestUser, and a password of TestPa$$w0rd!.
- Click OK.
- Click Yes on the certificate message.
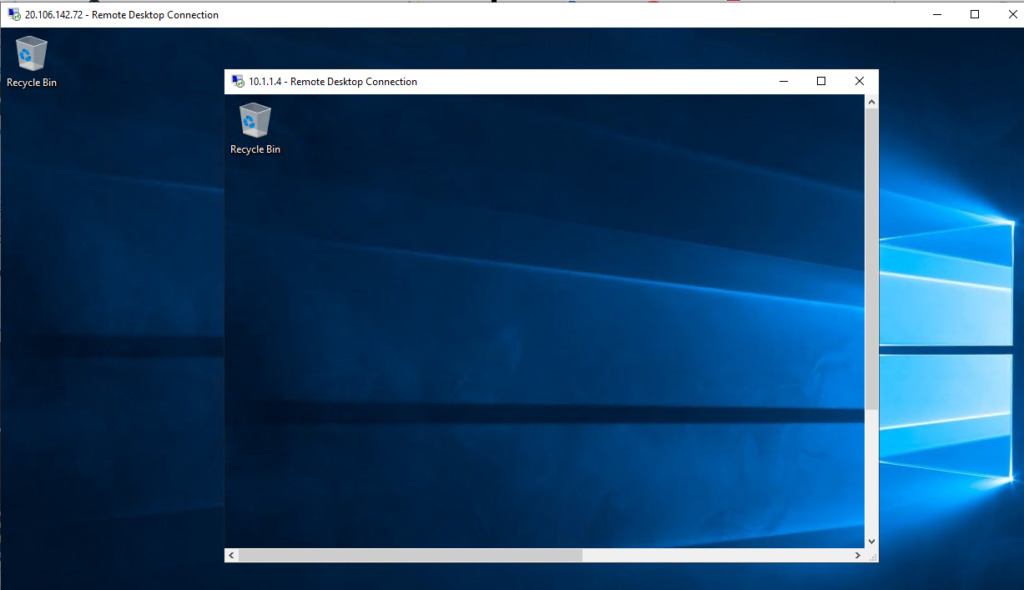
- So, now you have verified that the firewall network rule is working, as you have connected a remote desktop from one server to another server located in another virtual network.
- Close both RDP sessions to disconnect them.
Congratulations! You have configured, tested and secure your virtual hub via Azure Firewall Manager.
Reminder: Don’t forget to delete or shutdown all unused Azure resources after your labs for cost saving
Leave a Reply